Strategy: Page 5
-
Generative AI raises security concerns among IT leaders
Executives worry their organization lacks the ability to protect applications and workloads, according to a Flexential survey.
By Lindsey Wilkinson • Sept. 19, 2024 -
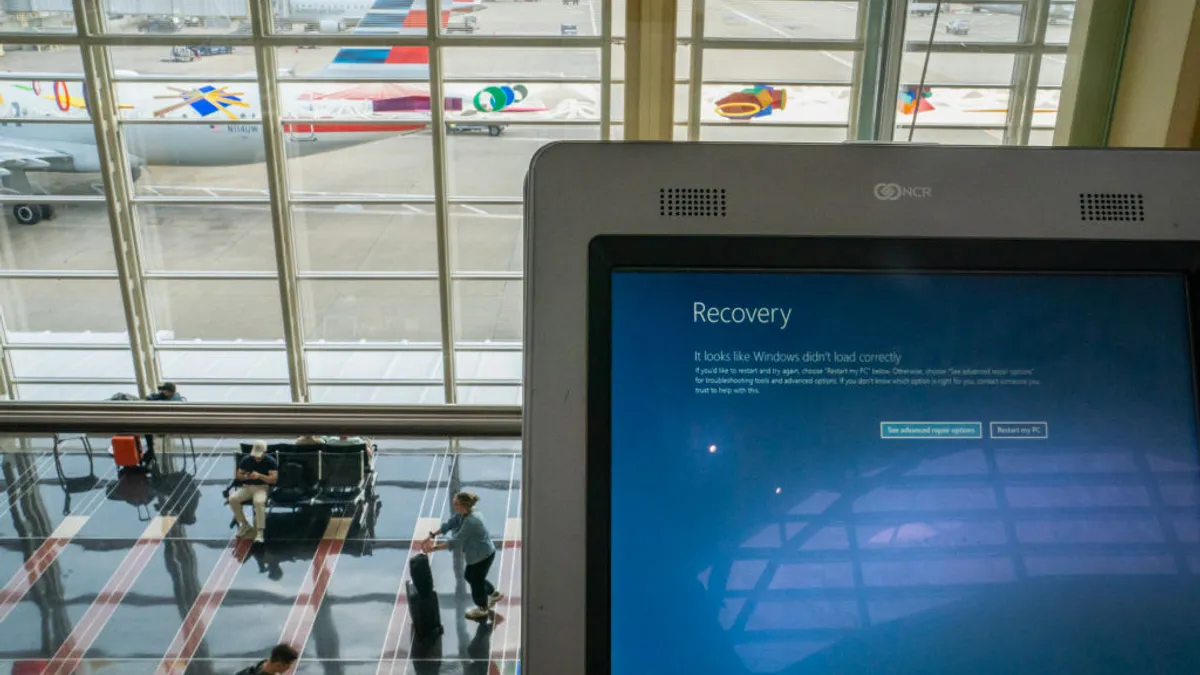
Port of Seattle official flags a cyber dilemma, ‘one-way street’ with federal agencies
A ransomware atttack disrupted the Seattle-Tacoma International Airport for weeks. Part of the problem, one official said, is that federal cyber recommendations are not timely.
By Matt Kapko • Sept. 19, 2024 -
 Explore the Trendline➔
Explore the Trendline➔
 .shock via Getty Images
.shock via Getty Images Trendline
TrendlineRisk Management
An esclation of cyber risks facing businesses and government has made cyber resilience a major priority.
By Cybersecurity Dive staff -
Open source maintainers, under security pressure, remain largely unpaid after XZ Utils
A report by Tidelift shows an equity gap remains between open source developers and well-resourced software users who are pushing for higher security standards.
By David Jones • Sept. 17, 2024 -
Sponsored by Tines
Enterprises are investing in AI copilots. But do they go far enough?
Enterprises are embracing AI copilots. But can they realize their impact?
By Eoin Hinchy, CEO and co-founder, Tines • Sept. 16, 2024 -
Microsoft, working with security partners, pledges better deployment, testing collaboration
Following a summit with U.S. and European partners, the company is working to build additional resiliency features to prevent a repeat of the historic global IT outage linked to CrowdStrike.
By David Jones • Updated Sept. 13, 2024 -
Mastercard’s $2.65B Recorded Future acquisition to buttress its security business
While Mastercard has cybersecurity oversight needs for its cards and payments businesses, it also sells security services to other companies, including banks and fintechs.
By Lynne Marek • Sept. 13, 2024 -
Most OT environments have at least 4 remote access tools, report finds
Claroty warned the prevalence of remote access tool sprawl, often linked to ransomware, raises the risk of malicious activity.
By David Jones • Sept. 12, 2024 -
Network security market breaks streak of declining growth in Q2: Dell’Oro Group
The rebound arrives as heightened levels of malicious activity are targeting firewalls, the largest product segment in the market.
By Matt Kapko • Sept. 12, 2024 -
How to manage the rising tide of CVEs
As the volume and complexity of vulnerabilities grows, organizations are struggling to manage and mitigate the security defects.
By Rosalyn Page • Sept. 11, 2024 -
Global cybersecurity workforce growth flatlines, stalling at 5.5M pros
ISC2’s annual report draws some troubling conclusions for the state of cyber defense. Budget cuts, layoffs and hiring freezes are exacerbating a global staffing shortage.
By Matt Kapko • Sept. 11, 2024 -
Security budgets continue modest growth, but staff hiring slows considerably, research finds
The report by IANS Research and Artico Search shows security priorities are clashing with economic realities.
By David Jones • Sept. 10, 2024 -
Cyber insurance keeps growing, as threats spur competition
Concerns remain about aggregation risk as highlighted by the July outage of Microsoft Windows devices, according to a report from Moody’s Ratings.
By David Jones • Sept. 9, 2024 -
Key cyber insurance stakeholders urge government to help close $900B in uncovered risk
Marsh McLennan and Zurich Insurance Group issued a white paper urging a public-private partnership to help tackle a growing coverage gap. The White House is working on a plan.
By David Jones • Sept. 6, 2024 -
White House launches cybersecurity hiring sprint to help fill 500,000 job openings
National Cyber Director Harry Coker Jr. unveiled the program as part of an effort to fill a continued gap in cyber, technology and AI positions.
By David Jones • Sept. 5, 2024 -
Infosec spending to hit 3-year growth peak, reach $212B next year: Gartner
The continuation of annual double-digit growth rates, 15% next year, comes as organizations consolidate spending and reassess EPP and EDR needs.
By Matt Kapko • Sept. 5, 2024 -
Microsoft is training developers on the intricacies of threat intelligence
Cybercrime wonk Sherrod DeGrippo is taking Microsoft’s software developers and engineers on a journey into her world, the depths of threat intelligence.
By Matt Kapko • Sept. 4, 2024 -

 Photo illustration by Danielle Ternes/Cybersecurity Dive; photograph by yucelyilmaz via Getty Images
Photo illustration by Danielle Ternes/Cybersecurity Dive; photograph by yucelyilmaz via Getty Images
CISA launches cyber incident reporting portal to streamline breach disclosure
The secure portal is designed to encourage faster and more robust information sharing about malicious attacks and critical vulnerabilities.
By David Jones • Aug. 30, 2024 -
CrowdStrike takes a revenue hit as global IT outage reckoning lingers
Sales are taking longer to close and the cybersecurity vendor is offering discounts to stem potential customer losses.
By Matt Kapko • Aug. 29, 2024 -
SentinelOne fields inquiries from new customers following global IT outage linked to CrowdStrike
Companies looking to diversify their risk from disruption are approaching SentinelOne, a week after similar customer movement was reported by Palo Alto Networks.
By David Jones • Aug. 28, 2024 -

 Photo illustration by Danielle Ternes/Cybersecurity Dive; photograph by yucelyilmaz via Getty Images
Photo illustration by Danielle Ternes/Cybersecurity Dive; photograph by yucelyilmaz via Getty Images
CISA officials credit Microsoft security log expansion for improved threat visibility
CISA officials say they plan to hold Microsoft accountable to ensure the company lives up to its commitments.
By David Jones • Aug. 27, 2024 -
Marketing data security threats are rising: Where CMOs see gaps
While marketers prioritize working with data security teams, effective communication remains a struggle, according to research from the CMO Council and KPMG.
By Peter Adams • Aug. 23, 2024 -
US, Australian authorities lead international push to adopt event logging
State-linked and criminal threat groups are using living-off-the-land techniques to hide their hacking activities behind regular security tools.
By David Jones • Aug. 22, 2024 -
After a wave of attacks, Snowflake insists security burden rests with customers
The cloud-based data warehouse vendor remains “slightly muted” about the attacks on its customers because it wasn’t breached, CEO Sridhar Ramaswamy said.
By Matt Kapko • Aug. 22, 2024 -
Insurance coverage drives cyber risk reduction for companies, researchers say
Companies with cyber coverage are better able to detect and respond to attacks, according to a Forrester report.
By David Jones • Aug. 21, 2024 -
Opinion
3 tips to building a robust AI security strategy
Organizations can reap bigger benefits from AI with guardrails that combine human oversight, strong underlying security architecture and technical controls.
By Anton Chuvakin • Aug. 21, 2024