Breaches
-
Dozens of Red Hat npm packages targeted in supply chain attack
Researchers said a variant of the Mini Shai-Hulud is involved in the compromise.
By David Jones • June 2, 2026 -
Iranian government, not hacktivist group, breached LA Metro system, security firm says
A report by Israel-based Gambit Security dismisses the hackers’ claims of being patriotic but unaffiliated activists.
By Eric Geller • May 26, 2026 -
 Explore the Trendline➔
Explore the Trendline➔
 Getty Images
Getty Images Trendline
TrendlineManaging identity sprawl
Cyber threat actors know the simplest way to hack into an enterprise and remain under the radar is with stolen, legitimate user credentials -- and cloud services and AI are making managing and securing digital identities more challenging than ever.
By Cybersecurity Dive staff -
Grafana Labs links GitHub environment breach to TanStack npm supply chain attack
The company behind the widely used observability platform refused an extortion demand and has since taken steps to harden its security.
By David Jones • May 21, 2026 -
7-Eleven hit by data breach
The retailer confirmed that an unauthorized third party gained access to certain systems used to store franchisee documents earlier this spring.
By Brett Dworski • May 20, 2026 -
Compromised coding tool helped hackers breach thousands of GitHub repositories
The attack is the latest example of hackers’ intense focus on open-source packages.
By Eric Geller • May 20, 2026 -
Grafana Labs says hacker gained access to codebase through leaked token
The company, which operates a widely used observability platform, is refusing to pay an extortion demand.
By David Jones • Updated May 19, 2026 -
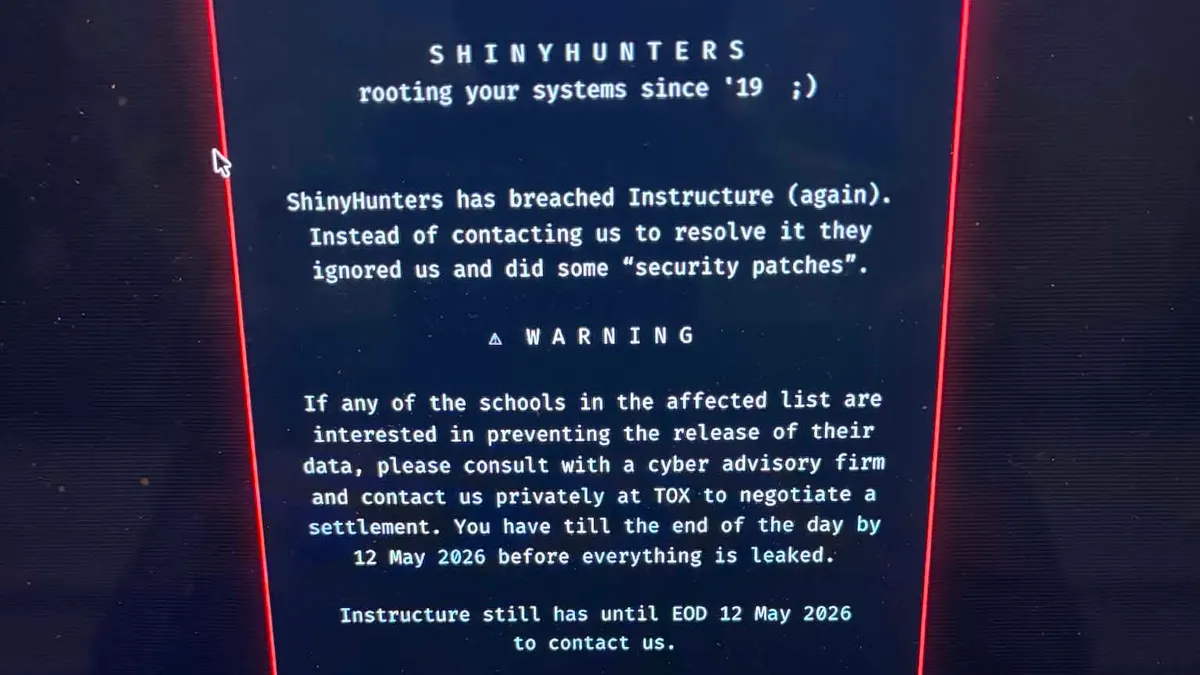
Second Canvas data breach causes major disruptions for schools, colleges
The Instructure-owned learning management system went offline on May 7 after a threat actor once again gained unauthorized access.
By Anna Merod • May 11, 2026 -
Businesses hide vast majority of ransomware attacks, report finds
The security firm BlackFog said the number of disclosed incidents it tracked in Q1 was roughly one-tenth of the number of undisclosed incidents.
By Eric Geller • May 7, 2026 -

 Retrieved from NASA's Moderate Resolution Imaging Spectroradiometer.
Retrieved from NASA's Moderate Resolution Imaging Spectroradiometer.
Iran-sponsored threat group behind false flag social engineering campaign
The state-linked actor has been masquerading as a criminal ransomware group in attacks targeting U.S. organizations.
By David Jones • May 6, 2026 -
Trellix investigating breach of source code repository
The cybersecurity company said there is no immediate evidence of code being exploited or released.
By David Jones • May 5, 2026 -
Major critical infrastructure supplier reports cyberattack
Itron, which makes devices that measure energy and water use, said its operations were continuing, despite the intrusion.
By Eric Geller • April 27, 2026 -
Hasbro expects March cyberattack to impact second-quarter revenue
The toymaker is reviewing files and working to fully bring certain systems back online. The company will incur some costs related to the investigation.
By David Jones • April 24, 2026 -
Vercel systems targeted after third-party tool compromised
An employee using a consumer app was breached after granting too many permissions.
By David Jones • April 20, 2026 -
NERC is ‘actively monitoring the grid’ following Iran-linked cyber threat
Hackers have disrupted critical U.S. infrastructure by targeting programmable logic controllers, the Cybersecurity and Infrastructure Security Agency warned.
By Robert Walton • April 9, 2026 -
US operation evicts Russia from hacked SOHO routers used to breach critical infrastructure
The newly disclosed cyberattack campaign is the latest evidence of the threat end-of-life routers pose to major organizations.
By Eric Geller • Updated April 9, 2026 -
Hims & Hers says limited data stolen in social engineering attack
The telehealth provider said hackers gained access to a third-party customer service platform, but medical records remained secure.
By David Jones • April 6, 2026 -
Cyberattack hits Hasbro, impacting orders and shipping
The major U.S. toymaker and entertainment company is still working to assess if company data was stolen in the attack.
By David Jones • Updated April 1, 2026 -
Iran-linked actors target Middle Eastern city governments to undermine missile-strike responses
The password-spraying campaign is the latest evidence that Iran is hitting back in cyberspace.
By Eric Geller • April 1, 2026 -
Stryker restores most manufacturing after cyberattack
The medtech company has been working to restore manufacturing, ordering and shipping operations since it was hit by a cyberattack on March 11.
By Ricky Zipp • March 30, 2026 -
‘Do not shift budgets to AI’: How businesses should and shouldn’t respond to evolving threats
Experts said companies rushing to buy AI services risk letting their existing, still-vital defensive measures deteriorate.
By Eric Geller • March 25, 2026 -
Companies face difficult choices in blaming hackers for an attack
Publicly naming a hacking group can affect everything from retaliation to insurance coverage.
By Eric Geller • March 24, 2026 -
Lockheed Martin targeted in alleged breach by pro-Iran hacktivist
The group is demanding millions of dollars to not sell the information to U.S. adversaries.
By David Jones • March 23, 2026 -
Stryker confirms cyberattack is contained and restoration underway
An assurance letter from Palo Alto Networks provides insight into the forensic investigation at the medical technology firm.
By David Jones • March 23, 2026 -
Telus Digital confirms hack as ShinyHunters claims credit for massive data theft
The Canadian business-process outsourcer, which counts many major businesses among its customers, still isn’t sure what the hackers stole.
By Eric Geller • March 16, 2026 -
Robotics firm Intuitive Surgical says cyberattack compromised business, customer data
The company said an intruder accessed employee information, customer contact details and other records.
By Ricky Zipp • March 16, 2026