Cyberattacks
-
Dozens of Red Hat npm packages targeted in supply chain attack
Researchers said a variant of the Mini Shai-Hulud is involved in the compromise.
By David Jones • June 2, 2026 -
CISA adds critical Palo Alto Networks firewall flaw to KEV as company, researchers warn of exploitation
The vulnerability in a vital defensive technology creates serious risks for federal networks, CISA said.
By Eric Geller • June 1, 2026 -
 Explore the Trendline➔
Explore the Trendline➔
 Getty Images
Getty Images
-
Iranian government, not hacktivist group, breached LA Metro system, security firm says
A report by Israel-based Gambit Security dismisses the hackers’ claims of being patriotic but unaffiliated activists.
By Eric Geller • May 26, 2026 -
Iran-linked hackers target key US, allied sectors with sophisticated spear-phishing messages
Companies, particularly those in the affected industries, should harden their defenses against impersonation schemes, Palo Alto Networks said.
By Eric Geller • May 22, 2026 -
Grafana Labs links GitHub environment breach to TanStack npm supply chain attack
The company behind the widely used observability platform refused an extortion demand and has since taken steps to harden its security.
By David Jones • May 21, 2026 -
Grafana Labs says hacker gained access to codebase through leaked token
The company, which operates a widely used observability platform, is refusing to pay an extortion demand.
By David Jones • Updated May 19, 2026 -
West Pharmaceutical starts restoring operations after ransomware attack
The company confirmed data was stolen and encrypted by the attackers.
By David Jones • May 14, 2026 -
Foxconn confirms cyberattack affecting some North American facilities
A ransomware group has claimed a major attack against the electronics manufacturer.
By David Jones • May 13, 2026 -
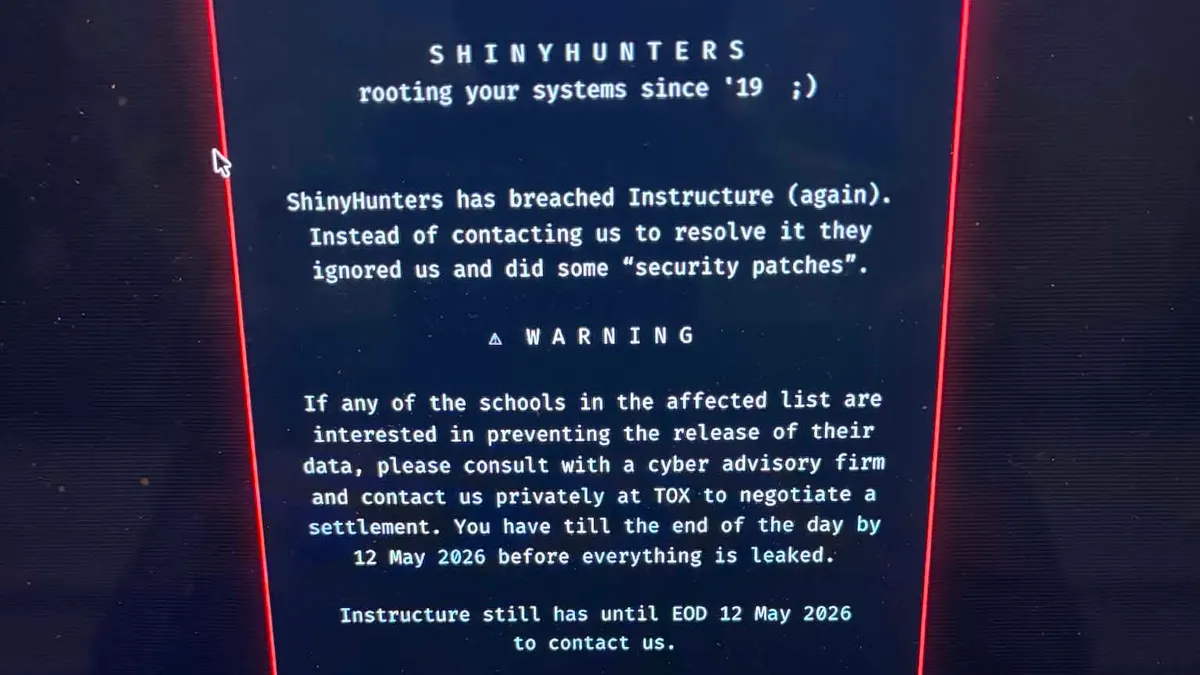
Canvas owner reaches ‘agreement’ with threat actors after data breach
Cybersecurity experts suggest that Instructure appears to have made a ransomware payment, which the FBI highly discourages.
By Anna Merod • May 13, 2026 -
Second Canvas data breach causes major disruptions for schools, colleges
The Instructure-owned learning management system went offline on May 7 after a threat actor once again gained unauthorized access.
By Anna Merod • May 11, 2026 -
Sponsored by SHI
Identity is the new perimeter as rapid NHI proliferation threatens visibility and control
NHIs are linked to diverse assets across the enterprise technology ecosystem, creating a highly fragmented architecture and making it challenging for security teams to maintain visibility and control.
May 11, 2026 -
Instructure confirms cybersecurity incident
The ed tech company that operates Canvas said information impacted by the data breach includes messages, names, email addresses and student ID numbers.
By Anna Merod • May 8, 2026 -
Anthropic’s Claude used in attempted compromise of Mexican water utility
Researchers warn the incident highlights how AI tools can help untrained threat actors develop complex cyberattack capabilities.
By David Jones • May 8, 2026 -
Businesses hide vast majority of ransomware attacks, report finds
The security firm BlackFog said the number of disclosed incidents it tracked in Q1 was roughly one-tenth of the number of undisclosed incidents.
By Eric Geller • May 7, 2026 -
Sponsored by 1Password
How OpenClaw’s agent skills become an attack surface
OpenClaw and similar AI agent ecosystems, present pressing security risks.
May 4, 2026 -
As email phishing evolves, malicious attachments decline and QR codes surge
A new Microsoft report also describes the collapse of a once-dominant tool for generating phishing websites with fake CAPTCHAs.
By Eric Geller • May 1, 2026 -
CISA adds Microsoft, ConnectWise vulnerabilities to active exploitation catalog
Russia has used one of the flaws, security experts said, while North Korea has used the other.
By Eric Geller • April 29, 2026 -
‘Fundamental tension’ undermines manufacturers’ cybersecurity
A simple security mistake caused roughly one-quarter of all financial losses in the sector in 2025, cybersecurity insurer Resilience said.
By Eric Geller • April 28, 2026 -
North Korea-linked actor targets Web3 execs in social-engineering campaign
Founders and other top executives were compromised to gain access to crypto wallets.
By David Jones • April 27, 2026 -
Major critical infrastructure supplier reports cyberattack
Itron, which makes devices that measure energy and water use, said its operations were continuing, despite the intrusion.
By Eric Geller • April 27, 2026 -
US, UK authorities warn that Firestarter backdoor malware survives patching
A federal agency was impacted by a hacking campaign that exploited flaws in Cisco devices.
By David Jones • April 27, 2026 -
China disguises cyberattacks with ‘covert network’ botnets, US and allies warn
A new security advisory highlights Beijing’s stealthy techniques.
By Eric Geller • Updated April 23, 2026 -
Deep Dive
Iran-nexus threat groups refine attacks against critical infrastructure
State-sponsored and hacktivist groups have shown greater determination to damage or disable energy, water and other key sectors.
By David Jones • April 23, 2026 -
Phishing — sometimes with AI’s help — topped initial-access methods in Q1, Cisco says
Hackers can now spin up fake login pages without writing a single line of code.
By Eric Geller • April 22, 2026 -
CISA urges security teams to view environments following axios compromise
A suspected North Korea-linked actor is behind a supply chain attack on the widely used library.
By David Jones • April 21, 2026