Vulnerability
-
Cisco warns zero-day flaw in SD-WAN is being exploited
The company cautioned that no current patches are available and the flaw could allow an attacker to conduct command injection attacks.
By David Jones • June 5, 2026 -
Anthropic shares Mythos with 150 more organizations, including critical infrastructure operators
The AI firm also said it’s exploring how to help open-source developers deal with a flood of vulnerability reports.
By Eric Geller • June 2, 2026 -
CISA adds critical Palo Alto Networks firewall flaw to KEV as company, researchers warn of exploitation
The vulnerability in a vital defensive technology creates serious risks for federal networks, CISA said.
By Eric Geller • June 1, 2026 -
Sponsored by SHI
Top 4 data security best practices for the AI-enabled enterprise
To maximize AI’s value without increasing security risk, organizations must enforce best‑practice data protections across their environment.
June 1, 2026 -
CISA urges security teams to check for software development compromises
The agency warned about a wave of attacks targeting credentials and other secrets across critical supply chains.
By David Jones • May 29, 2026 -
Leading AI models are more vulnerable to malicious prompts than vendors claim
Hackers could subvert frontier models with attacks that their developers overlook, Cisco said.
By Eric Geller • May 27, 2026 -
Patch bypass allows hackers to exploit prior flaw in SonicWall SSL-VPN
Researchers said a wave of attacks began in February targeting firewalls that appeared to be protected.
By David Jones • May 19, 2026 -
Deep Dive
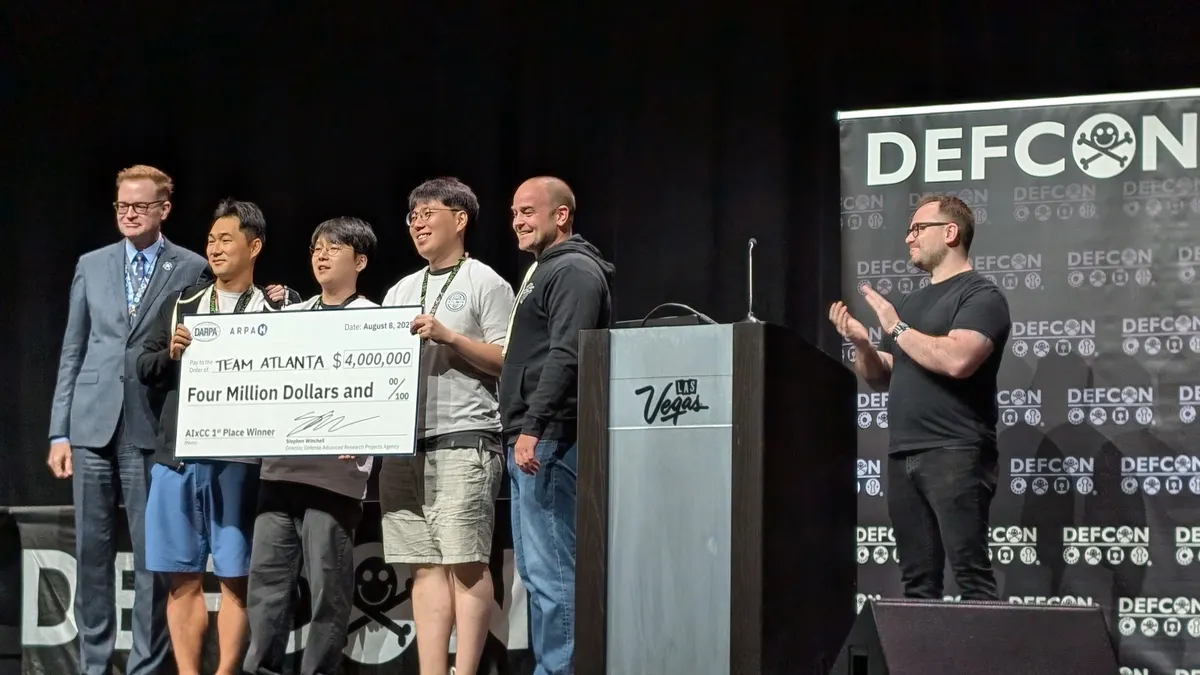
How a government contest launched a revolution in AI-based bug hunting
Security researchers have spent months honing AI systems that can find and fix serious vulnerabilities. Critical infrastructure everywhere could benefit.
By Eric Geller • May 18, 2026 -
Attackers exploit critical flaw in Cisco Catalyst SD-WAN Controller
Researchers discovered the authentication bypass vulnerability while investigating a prior issue in the same service.
By David Jones • May 15, 2026 -
Frontier AI models reap rapid discovery of security vulnerabilities
Security teams have just a few months before AI-driven exploitation becomes the norm, researchers warn.
By David Jones • May 14, 2026 -
OpenAI launches Daybreak to combat cyber threats
The cybersecurity initiative uses AI to detect software vulnerabilities, partnering with Cloudflare, Cisco and CrowdStrike to counter threats.
By Paige Gross • May 13, 2026 -
Identity takes center stage as a leading factor in enterprise cyberattacks
A new report shows two-thirds of ransomware attacks began with an identity-related breach.
By David Jones • May 12, 2026 -
AI used to develop working zero-day exploit, researchers warn
A report by GTIG shows threat groups are increasingly leveraging AI to scale attacks. The exploitation attempt was disclosed and patched, preventing a mass incident.
By David Jones • May 11, 2026 -
Palo Alto Networks warns state-linked cluster behind zero-day exploitation
A patch for the flaw, which hackers began targeting in early April, won’t be ready for another week.
By David Jones • May 7, 2026 -
Critical vulnerability in cPanel leads to widespread exploitation
Researchers warn that threat activity continues to surge, including brute force attacks and ransomware.
By David Jones • May 4, 2026 -
New MOVEit vulnerabilities prompt urgent patch warning
Progress Software warned customers to immediately upgrade the file-transfer tool to fix the serious flaws.
By Eric Geller • May 4, 2026 -
CISA adds Microsoft, ConnectWise vulnerabilities to active exploitation catalog
Russia has used one of the flaws, security experts said, while North Korea has used the other.
By Eric Geller • April 29, 2026 -
US, UK authorities warn that Firestarter backdoor malware survives patching
A federal agency was impacted by a hacking campaign that exploited flaws in Cisco devices.
By David Jones • April 27, 2026 -
AI-written software creates hassles for wary security teams
A new report explains what cybersecurity practitioners need to see before they trust AI coding tools.
By Eric Geller • April 23, 2026 -
Microsoft SharePoint vulnerability widely exposed across multiple countries
The disclosure comes just weeks after a prior SharePoint flaw was discovered.
By David Jones • April 22, 2026 -
CISA confirms exploitation of 3 more Cisco networking device vulnerabilities
Cisco revealed six critical flaws in widely used products in February. The government has now seen evidence that hackers are abusing four of them.
By Eric Geller • April 21, 2026 -
Vulnerability exploitation surges often precede disclosure, offering possible early warnings
Organizations can get ahead of major flaws with the right threat intelligence, according to a new report.
By Eric Geller • April 20, 2026 -
TP-Link routers face exploitation attempt linked to high-severity flaw
Researchers warn a potential botnet is targeting a vulnerability in end-of-life devices.
By David Jones • April 17, 2026 -
CIOs fret over rising security concerns amid AI adoption
AI is emerging as a critical tool and a growing threat as CIOs struggle to balance innovation with risk, according to a new report.
By Scarlett Evans • April 16, 2026 -

 R. Eskalis/NIST. Retrieved from NIST.
R. Eskalis/NIST. Retrieved from NIST.
NIST limits vulnerability analysis as CVE backlog swells
The agency will stop adding detailed information to vulnerabilities that don’t meet certain criteria.
By Eric Geller • April 16, 2026