Strategy: Page 28
-
It's time to bridge the gap between security and development
More than 80% of developers knowingly release applications with insecure code, but experts say security and development don't have to be at odds.
By Brian Eastwood • Aug. 9, 2021 -
CISA takes aim at information sharing woes, launches public-private super group
The Joint Cyber Defense Collaborative is Jen Easterly's first major initiative as CISA's second-ever director.
By Samantha Schwartz • Aug. 6, 2021 -
 Explore the Trendline➔
Explore the Trendline➔
 .shock via Getty Images
.shock via Getty Images Trendline
TrendlineRisk Management
An esclation of cyber risks facing businesses and government has made cyber resilience a major priority.
By Cybersecurity Dive staff -
Don't ask whether to pay a ransom — ask how attackers could get in
Paying a ransom does not always mitigate damage from the attack or unlock encrypted systems.
By Samantha Schwartz • Aug. 3, 2021 -

 Retrieved from Flickr/Amtec Photos.
Retrieved from Flickr/Amtec Photos.
Preparedness, checklists, leadership buy-in: How to build a rapid IT response
Navigating cyberattacks and outages means companies rely on IT leaders to respond quickly, as business continuity hinges on functioning systems.
By Roberto Torres • Aug. 2, 2021 -
Column
Behind the Firewall: 5 security leaders share incident response plans
With a strong plan in place, security teams can jump immediately into action when a cyber incident occurs to — hopefully — mitigate the damage.
By Katie Malone • July 30, 2021 -

 Photo illustration by Danielle Ternes/Cybersecurity Dive; photograph by yucelyilmaz via Getty Images
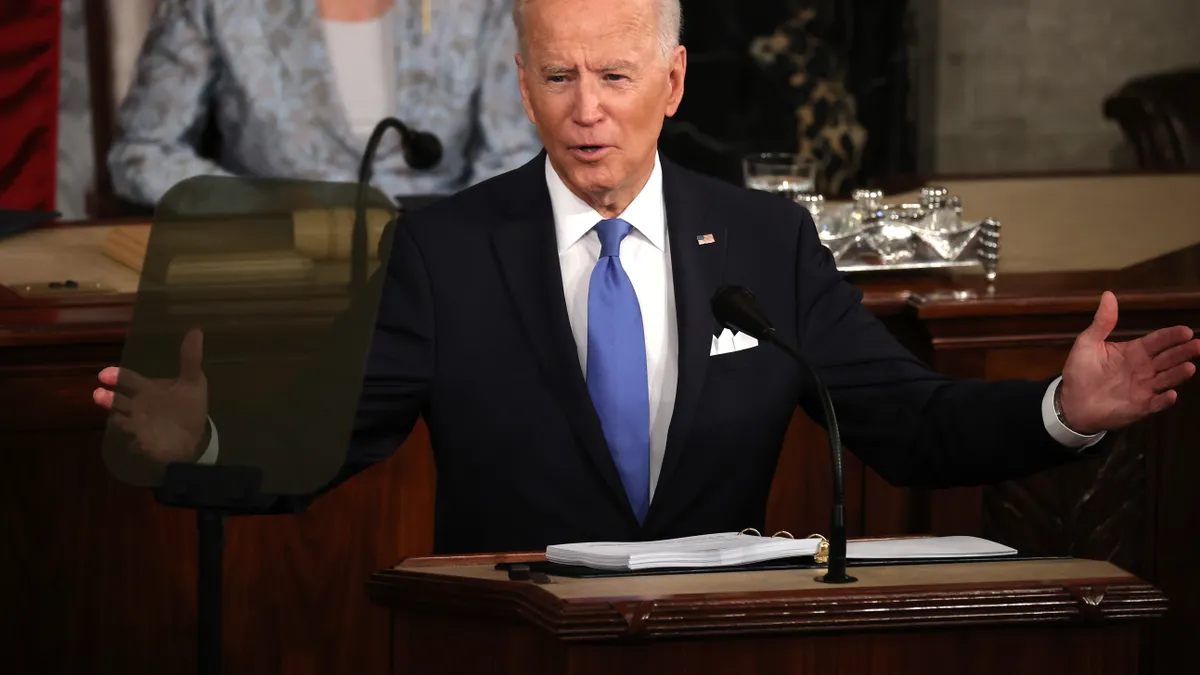
Photo illustration by Danielle Ternes/Cybersecurity Dive; photograph by yucelyilmaz via Getty Images White House cyber strategy takes shape
White House cyber strategy takes shapeBiden orders voluntary cybersecurity performance goals for electric utilities, other critical sectors
The president on Wednesday signed a national security memorandum that also expands and formally establishes a cross-sector Industrial Control System Cybersecurity Initiative, which was piloted by the electric sector.
By Robert Walton • July 30, 2021 -
Ransomware, supply chain attacks put cyber insurers on notice
Malicious cyber activity will force the insurance industry to raise premiums, raise standards and, in some cases, negotiate ransom payments, newly released data from Coalition shows.
By David Jones • July 28, 2021 -
Engineers need cybersecurity training, too
Companies will undergo a shift in cyber culture, eventually combining the data engineers and network security professionals use to search for vulnerabilities.
By Samantha Schwartz • July 22, 2021 -
White House cyber strategy takes shape
Biden administration readies 3 initiatives to curb ransomware
The government wants cybercriminals to think twice before instigating an incident and private industry to engage more.
By Samantha Schwartz • July 21, 2021 -
Column
Behind the Firewall: How 6 security execs screen vendors
In the wake of high-profile vendor attacks, security due diligence prior to signing a third-party contract is a must.
By Katie Malone , David Jones • July 16, 2021 -
Want to quickly recover from ransomware? Plan ahead
Security teams need to understand how the business will work when an attacker limits access to its systems.
By Katie Malone • July 15, 2021 -
Critical goods industries face existential ransomware decisions
For certain industries, the choice is between paying millions to settle a criminal extortion or allowing a catastrophic supply chain disruption.
By David Jones • June 30, 2021 -
Opinion
3 ways to assess the effectiveness of security awareness training
Failure to prove the effectiveness of a security awareness program can lower the executive support critical to ensuring participation in the program.
By Richard Addiscott • June 14, 2021 -
Bad actors hide in everyday IT tools, complicating detection
Security tools automatically block certain threats, yet there's often a larger intrusion detection teams and services need to weed out.
By Samantha Schwartz • June 9, 2021 -
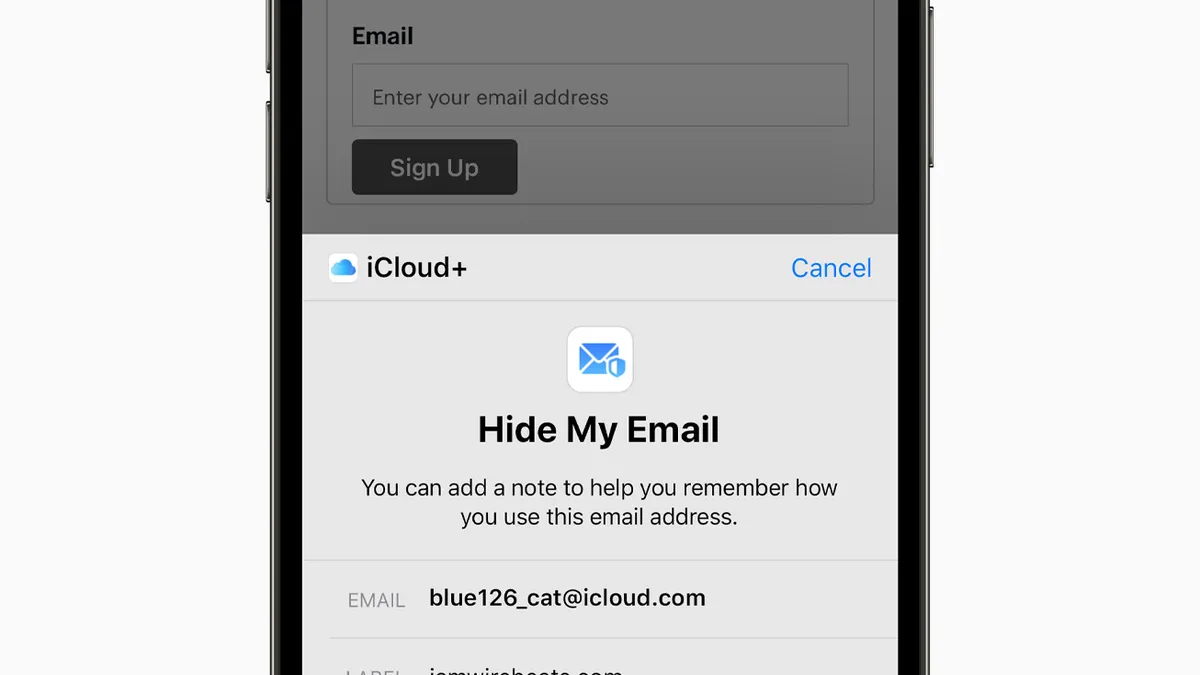
Apple's privacy, security features seen as favorable to enterprise remote work
Experts are comparing Private Relay to protections traditionally found in VPN technology, as Apple continues to grow its enterprise presence.
By David Jones • June 8, 2021 -
Data breaches, poor cyber practices raise cost of borrowing: study
Research from the American Accounting Association shows banks have raised interest rates on companies where customer data has been hacked.
By David Jones • June 7, 2021 -
CISOs earn higher profile with remote work, evolving threats
Corporate boards are demanding regular updates on the latest threats, while simultaneously asking CISOs to make sure workers meet business objectives in the most secure manner possible.
By David Jones • June 3, 2021 -
White House cyber strategy takes shape
Biden budget proposes $58B to take on legacy tech, cybersecurity
Legacy tech holds the federal government back, and agencies remain targets of advanced cyber crime. The budget proposal provides financial support to chip away at recovery.
By Katie Malone • June 3, 2021 -
Long-term SolarWinds consequences
Rethink risk management programs post-SolarWinds, experts say
Companies need to ensure their vendors are putting the most protections in place for their most important products and services.
By Samantha Schwartz • June 1, 2021 -
Sponsored by Axonius
The pandemic's impact on IT complexity, security priorities
A survey of IT security pros shed light on the pandemic’s impact on IT complexity & security trends.
By Mekhala Roy, Axonius • June 1, 2021 -
Column
Behind the Firewall: 4 cyber executives on security disasters they avoided
Cybersecurity leaders dodge catastrophes each day — from malware to gaps in the network perimeter.
By Katie Malone , David Jones , Samantha Schwartz • May 28, 2021 -
Beware open source when going zero trust, expert says
To combat software insecurities, begin with software inventory and a software bill of materials requirement.
By Samantha Schwartz • May 25, 2021 -
 "Government Accountability Office, Washington, DC, USA" by Cory Doctorow is licensed under CC BY-SA 2.0
"Government Accountability Office, Washington, DC, USA" by Cory Doctorow is licensed under CC BY-SA 2.0
Cyber premiums rise as insurers struggle to assess risk: GAO
Not only are insurers increasing premiums, they are lowering coverage limits "for certain perils," or types of cyberattacks, according to the report.
By Samantha Schwartz • May 24, 2021 -
How security and privacy can cultivate a relationship
Security and privacy are interwoven and layered throughout a company, motivated toward the end goal of data protection. Successful organizations recognize the overlap — and capitalize on it.
By Samantha Schwartz • May 20, 2021 -
What 5 security chiefs learned from COVID-19
From vaccine development to barren grocery story shelves, CISOs speaking at RSA Conference 2021 discussed how they navigated security in a complex threat landscape.
By Samantha Schwartz • May 19, 2021