Strategy: Page 27
-

 Photo illustration by Danielle Ternes/Cybersecurity Dive; photograph by yucelyilmaz via Getty Images
Photo illustration by Danielle Ternes/Cybersecurity Dive; photograph by yucelyilmaz via Getty Images
With remote work, any employee could be an insider threat. How is CISA mitigating the risk?
CISA released a self-assessment tool which organizations can use to generate reports on their tolerance and capabilities for preventing insider threats.
By Samantha Schwartz • Sept. 30, 2021 -
Remote work had little effect on employees' password habits: report
Employees are still reusing credentials, as vendors explore a passwordless future, according to a report from LastPass' Psychology of Passwords.
By Samantha Schwartz • Sept. 24, 2021 -
 Explore the Trendline➔
Explore the Trendline➔
 .shock via Getty Images
.shock via Getty Images Trendline
TrendlineRisk Management
An esclation of cyber risks facing businesses and government has made cyber resilience a major priority.
By Cybersecurity Dive staff -
Enterprises plan major investments as remote work escalates security risk: report
Companies face significant challenges in managing security as the work-from-home model moves from an emergency stopgap to a more permanent environment.
By David Jones • Sept. 22, 2021 -
Is there too much transparency in cybersecurity?
Between information sharing, software accountability, or incident response and disclosures, companies have to find the disclosure sweet spot.
By Samantha Schwartz • Sept. 21, 2021 -
What to know about software bill of materials
The Biden administration wants more transparency in the software supply chain. Will private industry join in?
By Samantha Schwartz • Sept. 20, 2021 -
Companies must develop operational plan for ransomware recovery
In the face of more frequent and sophisticated attacks, companies need to identify their most critical assets and work to limit cyberattack fallout.
By David Jones • Sept. 17, 2021 -
Companies confident in cybersecurity despite growing threats: report
There's a perception of "safety in numbers," Beazley's survey found. "Time will tell if such high levels of confidence are well placed."
By Samantha Schwartz • Sept. 16, 2021 -
Boards rethink incident response playbook as ransomware surges
Corporate boards are no longer rubber-stamping assurances from CIOs or CISOs but are bringing in outside experts, asking more questions and preparing for the risk of personal liability.
By David Jones • Sept. 15, 2021 -

 Bjork, Marten. Retrieved from Unsplash.
Bjork, Marten. Retrieved from Unsplash.
How companies can defend against credential theft
Unique passwords are the best defense against credential stuffing. But users, unless forced to act differently, will stick with what makes access easy.
By Sue Poremba • Sept. 14, 2021 -
InfoSec teams under pressure to compromise security for productivity: report
Younger workers are fueling a backlash against corporate security policies designed to protect companies from malicious attacks, a study from HP Wolf Security shows.
By David Jones • Sept. 9, 2021 -
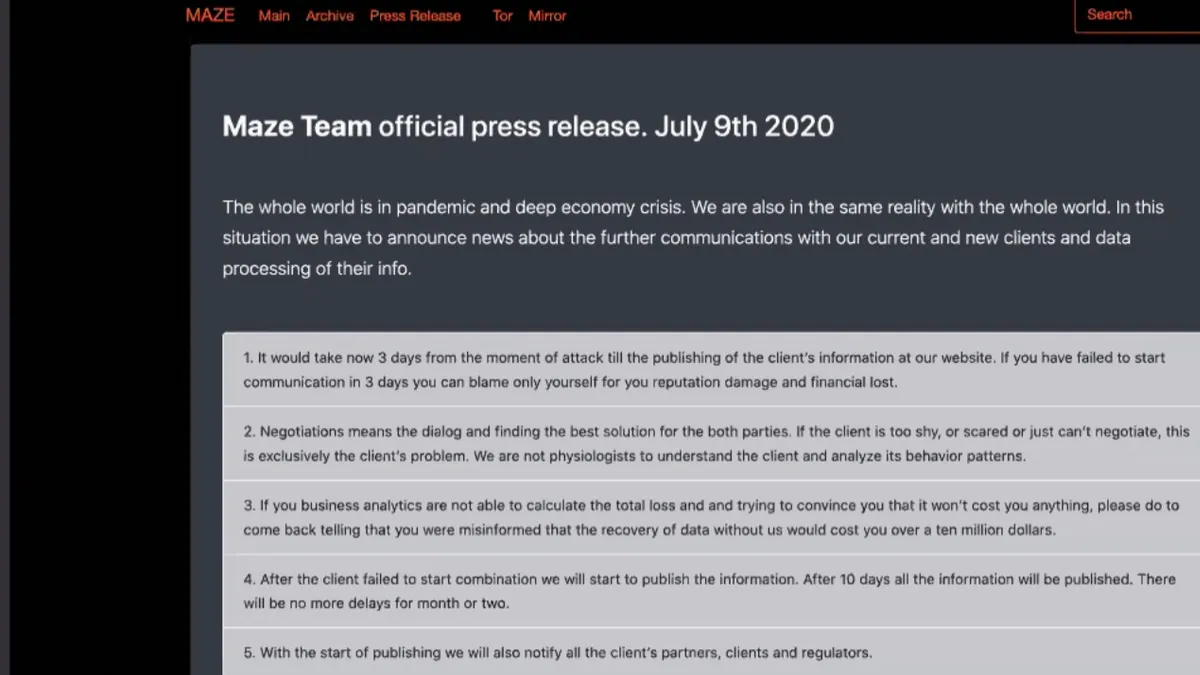
What ransomware negotiations look like
Fear can overwhelm the decision of whether to pay a ransom. But in negotiations, companies have to take a backseat.
By Samantha Schwartz • Sept. 9, 2021 -


iStock.com/pixelfit
 Sponsored by Code42
Sponsored by Code42Are you ready for the second wave of digital transformation?
In the second wave of digital transformation, understanding Insider Risk is more important than ever.
Sept. 7, 2021 -
Column
Behind the Firewall: What to do if your vendor has a security incident
A vendor with a checkered past with security incidents is not automatically disqualified from future contracts. Rather, there is a playbook for due diligence.
By Naomi Eide , Samantha Schwartz • Sept. 3, 2021 -
IT-OT crossover relitigates who is responsible for ICS security
If companies can effectively combine their IT and OT SOCs, they could be better equipped to uncover a fuller view of the kill chain.
By Samantha Schwartz • Sept. 2, 2021 -
What cyber insurance CEOs want to see from customers
Insurers joined high-profile CEOs at the White House summit last week to discuss how to improve national cybersecurity. For one insurance CEO, the industry needs three points of improvement.
By Samantha Schwartz • Aug. 31, 2021 -
Why a ban on ransom payments will not work
Those most impacted by an attack are motivated to pay. In some cases, it's not the victim company but its customers who want service restored.
By Samantha Schwartz • Aug. 27, 2021 -


Photo by MART PRODUCTION from Pexels

Companies are investing in security operations but limited by talent gaps
For some CISOs, the onus to attract talent is on them and the standards they make.
By Samantha Schwartz • Aug. 25, 2021 -
Opinion
Why most companies don't understand speed is vital to cybersecurity
In cybersecurity folk wisdom, frequent releases are scary and the foundation for security failure. Why is there this disconnect between cybersecurity superstition and reality?
By Kelly Shortridge • Aug. 24, 2021 -
In the event of a cyber incident, think like a lawyer
While security professionals may not be deeply involved in the legal aspects of a cyber incident, they have to be aware of attorney-client privileges.
By Samantha Schwartz • Aug. 17, 2021 -
Column
Behind the Firewall: Security investments that will stick post-pandemic
As long-term strategies for remote work solidify, VPNs, EDR and other tools are here to stay.
By Katie Malone , Samantha Schwartz • Aug. 16, 2021 -
Should healthcare organizations pay to settle a ransomware attack?
The decision goes beyond finances: In healthcare, it's a moral judgement, too. "I don't think there's a single yes or no," said Michael Coates, former Twitter CISO.
By Rebecca Pifer • Aug. 13, 2021 -
Criminal middlemen administer access to privileged accounts
Ransomware attacks stem from a specialized division of labor selling stolen credentials and providing unauthorized access to the enterprise, according to an IntSights report.
By David Jones • Aug. 12, 2021 -
White House cyber strategy takes shape
How the $1.2 trillion infrastructure bill invests in cyber
As part of the larger cyber funding injection, the legislation sets aside $100 million, allocated over five years, for the Cyber Response and Recovery Fund.
By Samantha Schwartz • Aug. 12, 2021 -
Is XDR the next best security solution?
SOCs are still learning about extended detection and response and how to apply it to an existing security stack. But when properly deployed, it's an asset for incident response.
By Samantha Schwartz • Aug. 11, 2021 -
How human instinct can interfere with cyber crisis response
In a gut reaction to a security incident, users may make the wrong move to avoid losing data.
By Samantha Schwartz • Aug. 10, 2021