Threats
-
Ransomware attacks increase against IT and food sectors
Social engineering and zero-day vulnerability weaponization are getting faster and easier, two information sharing and analysis centers said in new reports.
By Eric Geller • Feb. 13, 2026 -
CISA will shutter some missions to prioritize others
The agency has lost roughly one-third of its workforce since January 2025.
By Eric Geller • Updated 15 hours ago -
 Explore the Trendline➔
Explore the Trendline➔
 Getty Images
Getty Images Trendline
TrendlineRisk Management
An esclation of cyber risks facing businesses and government has made cyber resilience a major priority.
By Cybersecurity Dive staff -
CISA seeks infrastructure sector consultation on incident reporting rule
The agency is particularly interested in feedback on several aspects of the long-awaited regulation.
By Eric Geller • Feb. 12, 2026 -
SmarterMail facing widespread attacks targeting critical flaws
The business email and collaboration software is being exploited for potential ransomware.
By David Jones • Feb. 12, 2026 -


shutterstock.com/whiteMocca
 Sponsored by 10KMedia
Sponsored by 10KMediaThe Future of DAST in an AI-First World: Why Runtime Security Testing Remains Critical
Runtime validation is where the gap is widening—and where this shift creates the biggest leap forward.
By Joni Klippert, CEO of StackHawk • Feb. 12, 2026 -
Extortion attacks on the rise as hackers prioritize supply-chain weaknesses
Consulting firms and manufacturing companies accounted for many of the ransomware victims posted to the dark web in 2025, Intel 471 said.
By Eric Geller • Feb. 11, 2026 -
Polish power grid hack offers lessons for critical infrastructure operators, CISA says
The agency listed several steps businesses could take to prevent similar cyberattacks.
By Eric Geller • Feb. 10, 2026 -
FTC data highlights online threats to consumers and businesses
The commission listed several steps companies can take to fend off attacks.
By Eric Geller • Feb. 9, 2026 -
Ransomware attacks against education sector slow worldwide
The U.S. saw the highest number of education-related ransomware attacks in 2025, at 130, despite a 9% decline year over year.
By Anna Merod • Feb. 6, 2026 -
CISA orders feds to disconnect unsupported network edge devices
The government is worried about hackers accessing systems through insecure and poorly monitored routers, firewalls and similar equipment at the network perimeter.
By Eric Geller • Feb. 5, 2026 -
Asian government’s espionage campaign breached critical infrastructure in 37 countries
The victims included national telecommunications firms, finance ministries and police agencies, with most targets suggesting an economic focus, Palo Alto Networks said.
By Eric Geller • Feb. 5, 2026 -
Autonomous attacks ushered cybercrime into AI era in 2025
Malwarebytes urged companies to adopt continuous monitoring and lock down identity systems as AI models get better at orchestrating intrusions.
By Eric Geller • Feb. 4, 2026 -
React2Shell exploitation undergoes significant change in threat activity
Researchers see a sudden consolidation of source IPs since late January.
By David Jones • Updated Feb. 4, 2026 -
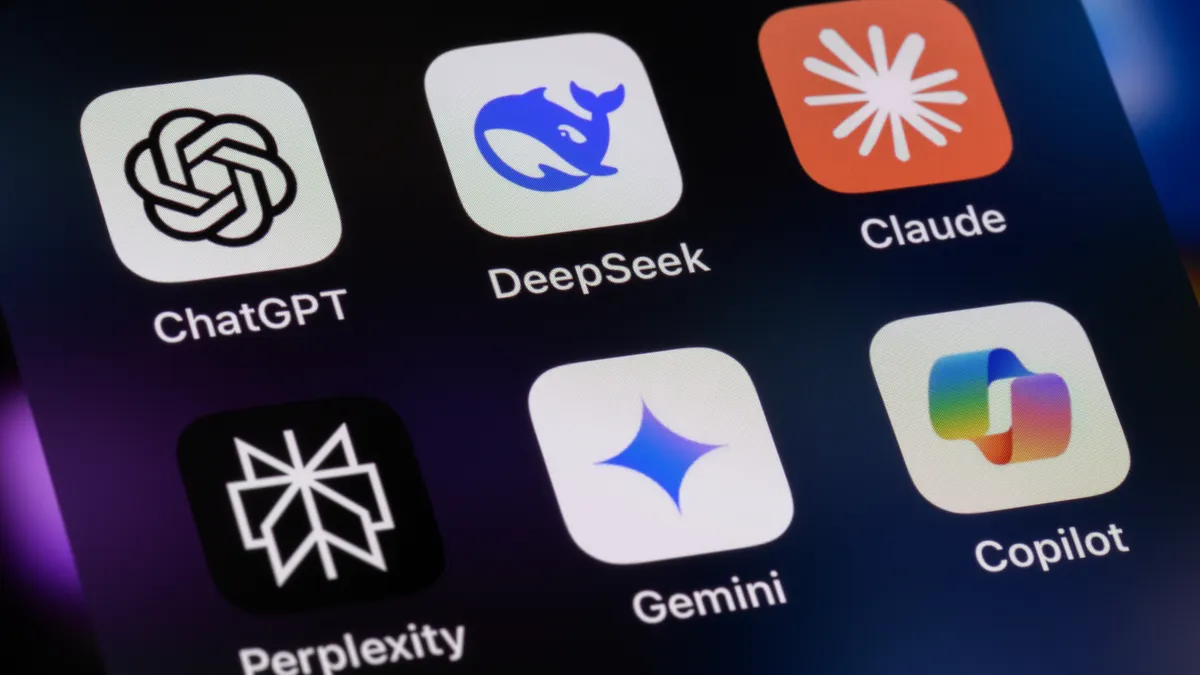
AI-ISAC inches forward under Trump administration
The U.S. government is exploring different options for how the information-sharing organization should work, an official said.
By Eric Geller • Feb. 3, 2026 -
ShinyHunters escalates tactics in extortion campaign linked to Okta environments
Researchers are tracking multiple clusters that are using social engineering to gain access to victims.
By David Jones • Feb. 2, 2026 -
FCC urges telecoms to boost cybersecurity amid growing ransomware threat
The commission said it was aware of ransomware disruptions at a growing number of small and medium-sized telecoms.
By Eric Geller • Feb. 2, 2026 -
Sponsored by Modulate
Voice channels are the next major attack vector that security teams can’t monitor
Deepfake voices, live fraud, zero visibility: why voice channels are the next security blind spot.
By Mike Pappas, CEO & Co-founder, Modulate • Feb. 2, 2026 -
Cisco sees vulnerability exploitation top phishing in Q4
The company’s recommendations included monitoring for abuses of multifactor authentication, a growing threat to the enterprise.
By Eric Geller • Jan. 30, 2026 -
Deep Dive
Manufacturers fortify cyber defenses in response to dramatic surge in attacks
IT/OT convergence and other trends are making the manufacturing industry’s networks more vulnerable and more frequently targeted, but sector leaders are working to improve their cyber posture.
By Eric Geller , David Jones • Jan. 29, 2026 -
CISA, security researchers warn FortiCloud SSO flaw is under attack
The exploitation activity comes weeks after a similar authentication bypass vulnerability was found.
By David Jones • Jan. 29, 2026 -
Interconnectedness, extortion risk make cybersecurity a healthcare C-suite priority
A new report from Trellix reviews the biggest breaches, describes the most effective defenses and profiles the most dangerous attackers.
By Eric Geller • Jan. 27, 2026 -
Cybercrime group claims credit for voice phishing attacks
Security researchers at Okta previously disclosed a social engineering campaign involving custom phishing kits.
By David Jones • Updated Jan. 27, 2026 -
Sponsored by Cisco Duo
Top 3 factors for selecting an identity access management tool
Identity and access management (IAM) ensures that people and entities with digital identities have the right level of access to your enterprise resources.
Jan. 26, 2026 -
Deep Dive
5 cybersecurity trends to watch in 2026
Corporations across the globe are facing a dynamic risk environment, as AI adoption surges with few guardrails, business resilience takes center stage and the insurance industry raises major concerns about the U.S. cyber market.
By David Jones • Jan. 23, 2026 -
IT teams aren’t equipped to stop rogue AI agents
Autonomous systems represent an attack surface existing cybersecurity services models aren’t designed to protect.
By James Anderson • Jan. 22, 2026