Page 2
-
Grafana Labs says hacker gained access to codebase through leaked token
The company, which operates a widely used observability platform, is refusing to pay an extortion demand.
Updated May 19, 2026 -
Attackers exploit critical flaw in Cisco Catalyst SD-WAN Controller
Researchers discovered the authentication bypass vulnerability while investigating a prior issue in the same service.
-
Frontier AI models reap rapid discovery of security vulnerabilities
Security teams have just a few months before AI-driven exploitation becomes the norm, researchers warn.
-
West Pharmaceutical starts restoring operations after ransomware attack
The company confirmed data was stolen and encrypted by the attackers.
-
Foxconn confirms cyberattack affecting some North American facilities
A ransomware group has claimed a major attack against the electronics manufacturer.
-
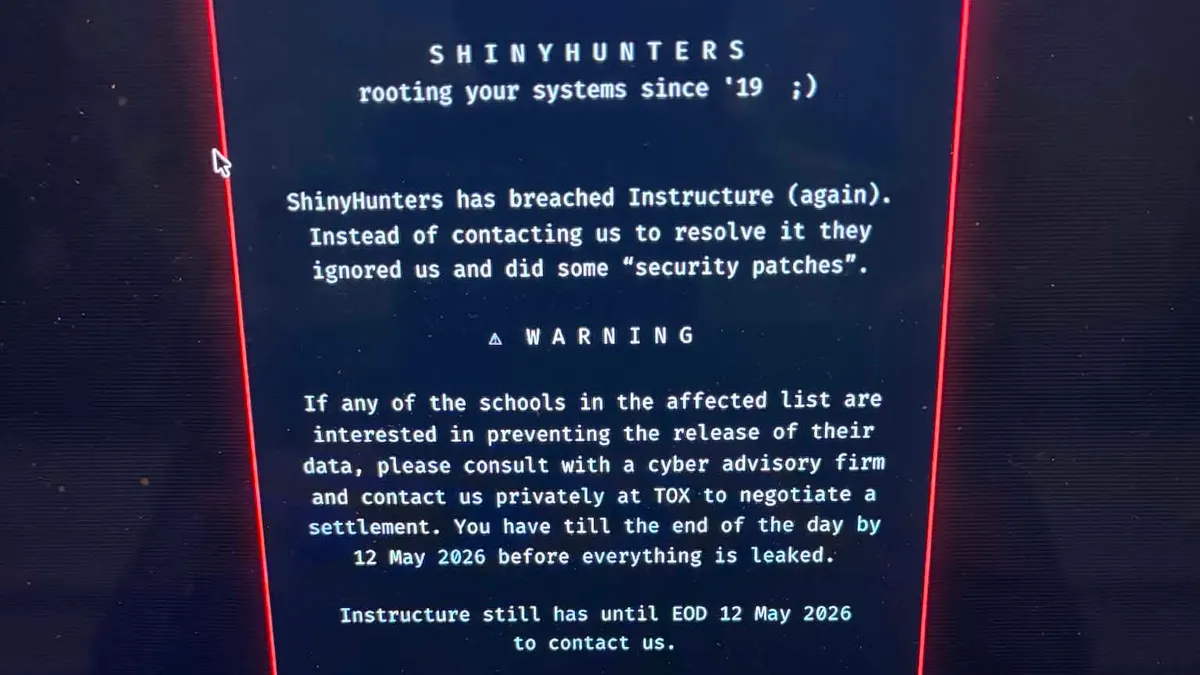
Instructure confirms cybersecurity incident
The ed tech company that operates Canvas said information impacted by the data breach includes messages, names, email addresses and student ID numbers.
-
OpenAI launches Daybreak to combat cyber threats
The cybersecurity initiative uses AI to detect software vulnerabilities, partnering with Cloudflare, Cisco and CrowdStrike to counter threats.
-
AI and an absent government: Takeaways from RSAC 2026
Cybersecurity professionals discussed the balance between autonomy and oversight at the recent conference.
-
Identity takes center stage as a leading factor in enterprise cyberattacks
A new report shows two-thirds of ransomware attacks began with an identity-related breach.
-
Deep Dive
New cybersecurity industry coalition aims to lead US critical infrastructure protection
The new Alliance for Critical Infrastructure’s biggest goal: changing how the nation plans for a major cybersecurity crisis.
-
Anthropic’s Claude used in attempted compromise of Mexican water utility
Researchers warn the incident highlights how AI tools can help untrained threat actors develop complex cyberattack capabilities.
-
AI used to develop working zero-day exploit, researchers warn
A report by GTIG shows threat groups are increasingly leveraging AI to scale attacks. The exploitation attempt was disclosed and patched, preventing a mass incident.
-
Second Canvas data breach causes major disruptions for schools, colleges
The Instructure-owned learning management system went offline on May 7 after a threat actor once again gained unauthorized access.
-
Palo Alto Networks warns state-linked cluster behind zero-day exploitation
A patch for the flaw, which hackers began targeting in early April, won’t be ready for another week.
-

 Retrieved from NASA's Moderate Resolution Imaging Spectroradiometer.
Retrieved from NASA's Moderate Resolution Imaging Spectroradiometer.
Iran-sponsored threat group behind false flag social engineering campaign
The state-linked actor has been masquerading as a criminal ransomware group in attacks targeting U.S. organizations.
-
Businesses hide vast majority of ransomware attacks, report finds
The security firm BlackFog said the number of disclosed incidents it tracked in Q1 was roughly one-tenth of the number of undisclosed incidents.
-

 R. Eskalis/NIST. Retrieved from NIST.
R. Eskalis/NIST. Retrieved from NIST.
NIST will test three major tech firms’ frontier AI models for cybersecurity risks
After Anthropic’s announcement of Claude Mythos, agencies across the government are racing to get ahead of new AI models’ potential dangers.
Updated May 21, 2026 -
Businesses eager but unprepared for AI to transform their security strategies
Meanwhile, a new report found, companies are neglecting other basic security tools.
-
CISA urges critical infrastructure firms to ‘fortify’ before it’s too late
As concerns mount about potential cyber sabotage by the Chinese government, the U.S. is warning operators to practice maintaining services in a degraded state.
Updated May 5, 2026 -
Trellix investigating breach of source code repository
The cybersecurity company said there is no immediate evidence of code being exploited or released.
-
New MOVEit vulnerabilities prompt urgent patch warning
Progress Software warned customers to immediately upgrade the file-transfer tool to fix the serious flaws.
-
Critical vulnerability in cPanel leads to widespread exploitation
Researchers warn that threat activity continues to surge, including brute force attacks and ransomware.
-
White House questions tech industry on defensive AI use, cybersecurity resilience
Companies may be reluctant to answer some of the government’s questions, given the sensitive topics they address.
-
US and allies urge ‘careful adoption’ of AI agents
New guidance from a coalition of Western governments underscores the difficult-to-predict risks of still-evolving agentic tools.
-
As email phishing evolves, malicious attachments decline and QR codes surge
A new Microsoft report also describes the collapse of a once-dominant tool for generating phishing websites with fake CAPTCHAs.